WPA/WPA2-PSK Cracking Solution
Introduction
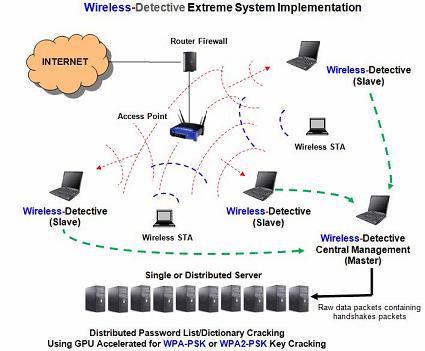
Decision Computer Group introduces WPA-PSK (TKIP) and WPA2-PSK (AES) cracking module which is available. This module allows recovery of WAP-PSK (TKIP) and WPA2-PSK (AES) password/key, especially some weak passwords consisting of words and phrases in spoken language. By utilizing Wireless-Detective system or other sniffer tools to capture the raw data packets containing the handshakes packets, user can use this WPA/WPA2-PSK cracking module to recover the password/key. The password/key obtained can then be used for the decryption, decoding and reconstruction of the WPA raw data collected.
Operation and Functionality
Password List or Dictionary Attack
This WPA/WPA2-PSK cracking module can utilize a single server or computer or utilize multiple (distributed) servers or computers to perform password list or dictionary (which can be customizable) attack to recover the password/key. A single server can process a single password or dictionary list. Depending on the number of password or dictionary lists available, user may use multiple servers, each processing a single password or dictionary list to run the recovery process. Decision can provide 10 password lists.
Distributed or Multiple System Architecture
A single server can process a single password or dictionary list. Depending on the number of password or dictionary lists available, user may use multiple servers, each processing a single password or dictionary list to run the recovery process. Decision can provide 10 password lists. By using multiple servers and multiple password or dictionary lists, speed of cracking and chance of obtaining the key can be increased.
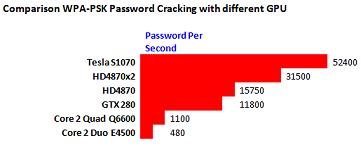
Hardware or GPU Acceleration
Acceleration of password/key recovery process can be done by utilizing hardware acceleration or GPU acceleration method. This method makes use of graphic cards to accelerate the cracking process, which could be 30 times faster than normal quad-core Intel CPU per card. Some graphic cards from NVIDIA and ATI are supported.
Compatibility
This WPA/WPA2-PSK cracking module is compatible and work with Wireless-Detective system. It also accepts raw data packets (with handshake packets) in PCAP or tcpdump format captured by using other sniffer tools.
Note:
Time required for cracking the WPA/WPA2-PSK always depends on the randomness (number only, alpha-numerical or full ASCII characters) and length of the password/key. It also depends on the quantity and quality of hardware or servers used for the password/key recovery process.
|